Like anything I participate in I inevitably take side quests. It turns out that this particular detour on LLSC26 happened almost instantly after launch. Whatever that says about my attention span I can't hear over the sound of my beautiful little red music square. Oh how I've missed my Zune! It's such a silly thing to be attached to but it's one of those formative pieces of technology that I got early on and I think it really helped shape my love for both music and technology. My first one I got in middle school, I think I was about 12, and it was an oblique black brick of a device. Everything about it save for the hard drive was built like a tank and I treated it like an absolute monster. And it comes as no surprise that that device eventually broke and I lost a collection of music I cared deeply about and then had to sit with the discomfort of not having it until my parents surprised me with one of the 120GB zunes later down the line.
I tried my damnedest to treat that one with care, and it lasted all through high school and into college, until it fell out of my pocket on the way to a biology lecture. I remember already being grumpy about the lecture, I was going to school for history and just didn't care about filling out the general curriculum, but the absolute devastation I felt after breaking my second and last Zune is something I can still feel. It's so silly to let material things bother you so much, but I had had this particular MP3 player for so many years, having it die on me a second time just hurt.
I never replaced it. By the time it broke it was already becoming a bit anachronistic to use a dedicated MP3 player, early Android phones could fill that role and I had a PSP that could also. There were options readily available and they attempted to fill the Zune sized hole in my heart. And so it should come as no surprise that that broken little Zune kicked around my technology junk drawer for many many many years, silently mourned but never really laid to rest. And of course as I'm considering LLSC and my not so old but old enough lab, I had to dig the Zune out. (Side note, I sympathize with everyone's commentary about Server 2008R2 being not that old, but seriously it was ~17 years ago guys. I'm not happy about that either!)
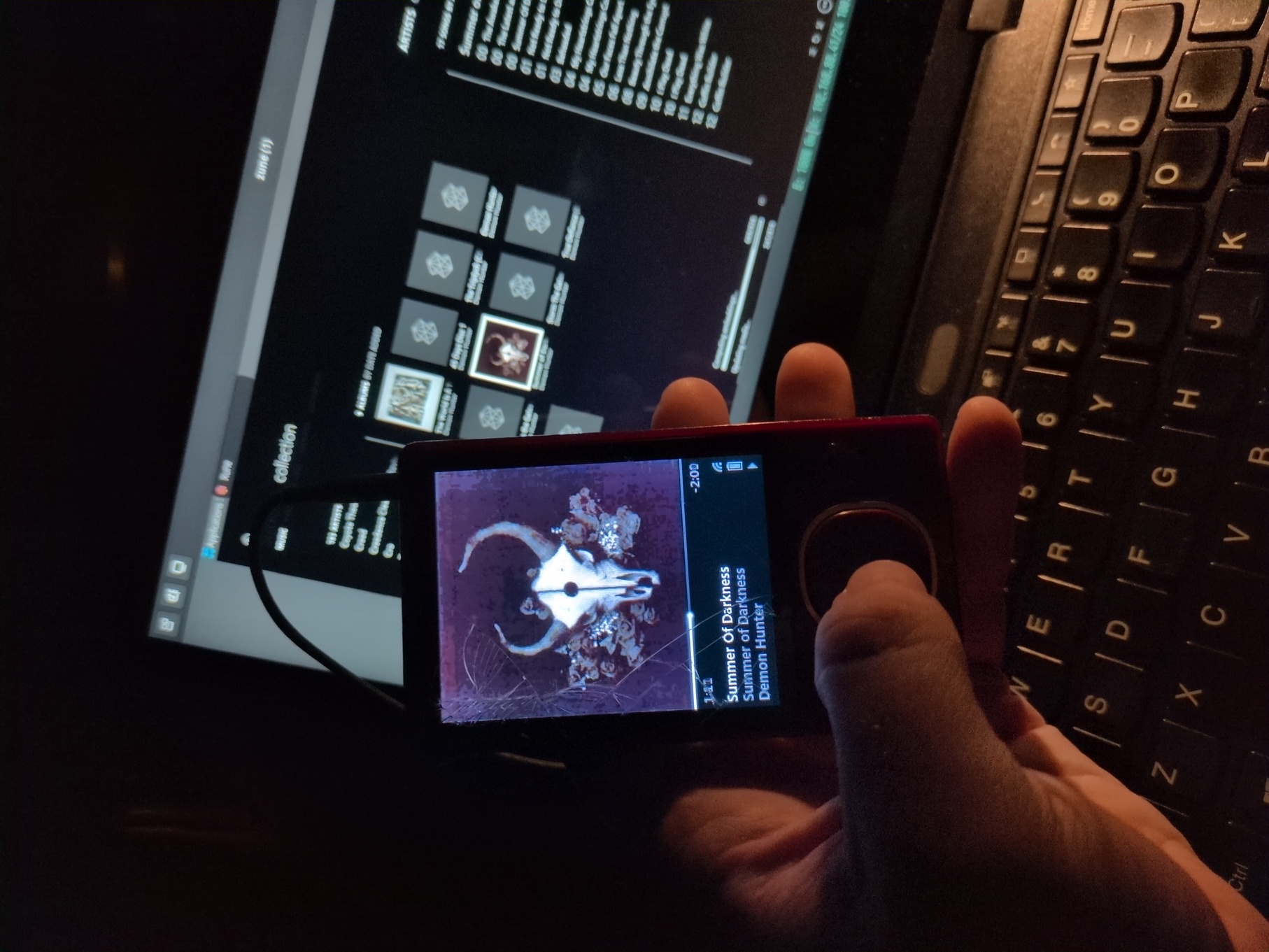
Here in all its glory, my last and only remaining Zune!

I tried to find the photos I took when I attempted to repair it extremely poorly a few years ago. I remember the process to crack the case open was frustrating, and I know for a fact that I damaged the case's clips when I did it because the Zune bulges in strange places and there's definitely some glue holding things back together. But the little hard drive in it and re-soldering the battery weren't particularly hard tasks. Of course with how badly damaged this Zune is it has never really mattered that it looked uglier to me, I really only cared about it holding together enough to be usable. And it is!

For those curious about the song it's "Bipolar Mind" by Chunk! No, Captain Chunk! a really good late 2000's French rock band, on the heavier side sort of like Four Year Strong. There's a ton of nuanced treble to their songs and I find that the tracks on music.youtube.com don't really do the music justice, they just don't sound the same on my Zune as they do on an Android phone. The DAC inside of the Zune is just really freaking good and stands up to time. At least in my opinion, I think from a technical perspective it's not as good as a modern DAP or DAC but it's a whole heck of a lot better than a general audio device. What you hear on a Zune tends to have a really full sound stage with punchy bright audio, the result of that is that it sounds really natural.
That bright and punchy audio is produced by this itty bitty chip on the Zune's motherboard. This is a photo of a 4GB or 8GB Zune rather than the 120GB. I can't find a picture of the 120GB motherboard unfortunately, but they all use a similar serious of Wolfson DACs for audio and power management.
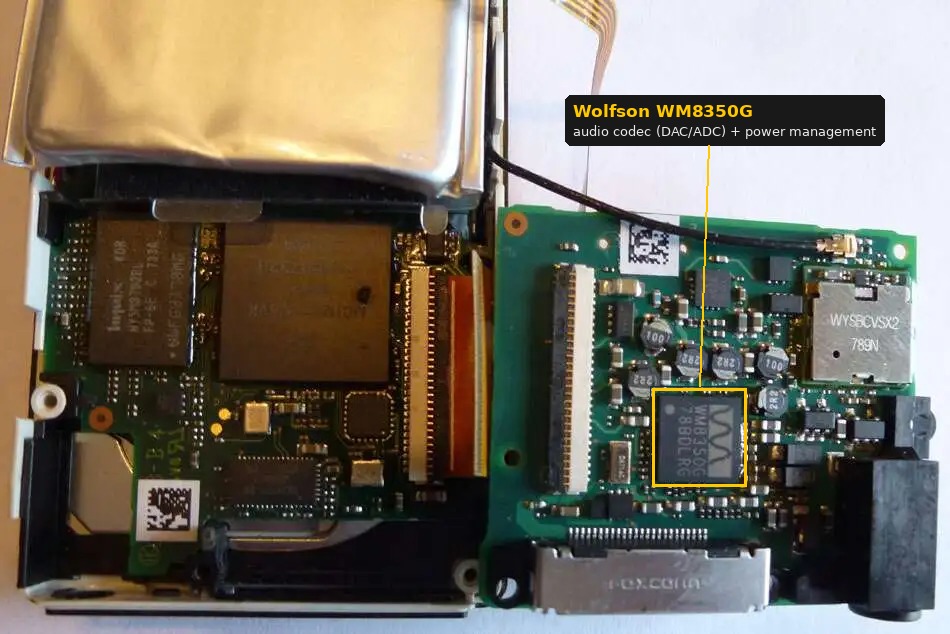
And it's this combination of audio and power management that really made the difference, the Wolfson DAC isn't some kind of magic chip that "makes the music sound good". Under the hood the DAC is just converting what's essentially a long collection of wavelength measurements and converting it into an electrical signal that gets pushed out your headphones. Being able to directly control power output based on the audio processing results in a more faithful reproduction of the actual sound wave. From a listeners perspective the result of this is that you experience the music a little more richly. Your noise floor is different when audio is reproduced by a high quality DAC using clean properly modulated power, when your noise floor is lower the background "hiss" of silence drops and you can pick up more nuanced tones, like the reverberation of a room. For the genre of music that I love the most, and was 90% of what I listened to when got and used my Zune, all of this matters insanely. You take something like Meshuggah or Demon Hunter where you have lots of heavy layered tones and the quality of your sound stage really matters, it literally defines how cleanly you can hear things instead of them falling into erroneous noise. Now all of that said the Wolfson DACs were also used in the 5th gen iPods and those sound different than a Zune! So there's a little bit of software engineering that goes into what you hear as well.
All of this is in a way an explanation of why something "useless" from a conventional standpoint would remain in my possession for so long. Really, it's just hard to replace something with that was literally transformative in how I heard music. Unfortunately software becomes obsolete and for a long time I dual booted Vista, then Windows 7 and 8.1 in a vein attempt to keep around a working copy of the Zune media management software that allowed me to use this beautiful little device. That became harder and harder as time went on, and various community efforts sprung up to hack together support for it, but it was never as effective as I wanted it to be. So sadly the little device found a resting place in my junk drawer until this year when I decided to revisit anachronism for a bit, I figured I could charge it and maybe load something onto it from my Vista netbook, for old times sake.
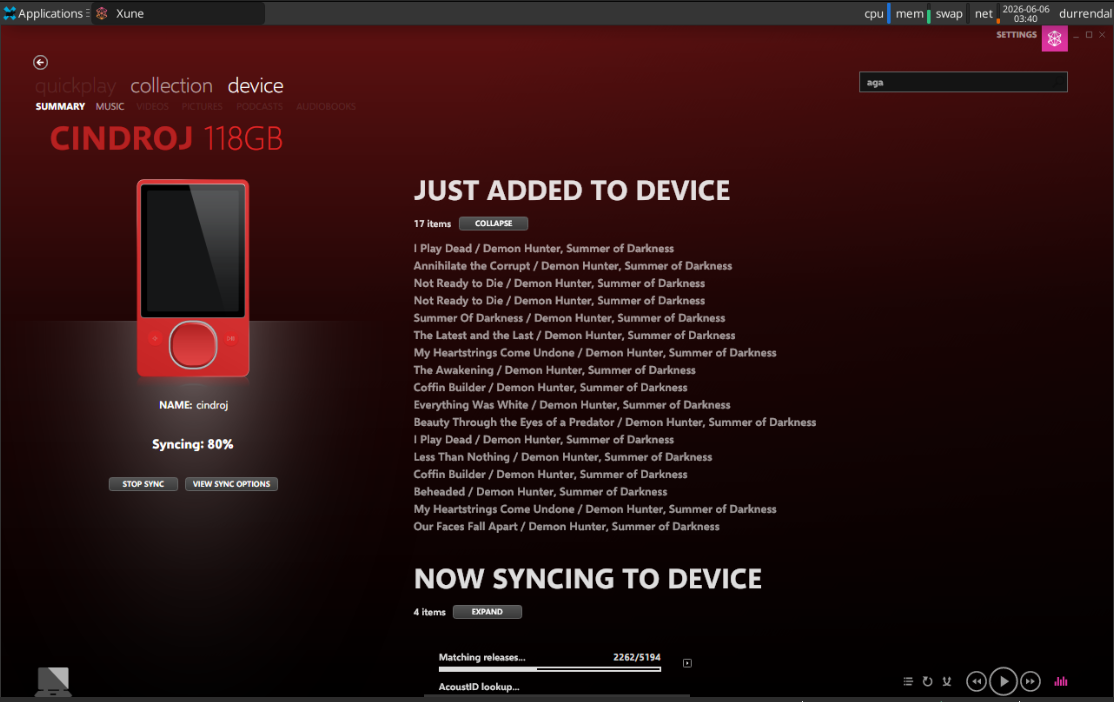
Imagine then my joy and surprise when I stumbled across Xune an early alpha release of the Zune software rewritten from the ground up in a way that not only allows it to run on Linux systems, but adds advanced media management functionality such as deduplication and automated identification of tracks! Literally an answer to an unspoken prayer, I can very literally reclaim my Zune as my primary MP3 player thanks to this project!
And I have! Instead of doing anything productive for LLSC I instead spent the entire last week migrating, deduplicating, and transcoding my music on my NAS and wiring up Xune in a dedicated Alpine VM on my Incus cluster so that it can chew on all of my media for as long as it needs to fully process the nearly 12000 songs I've managed to accumulate over the years.
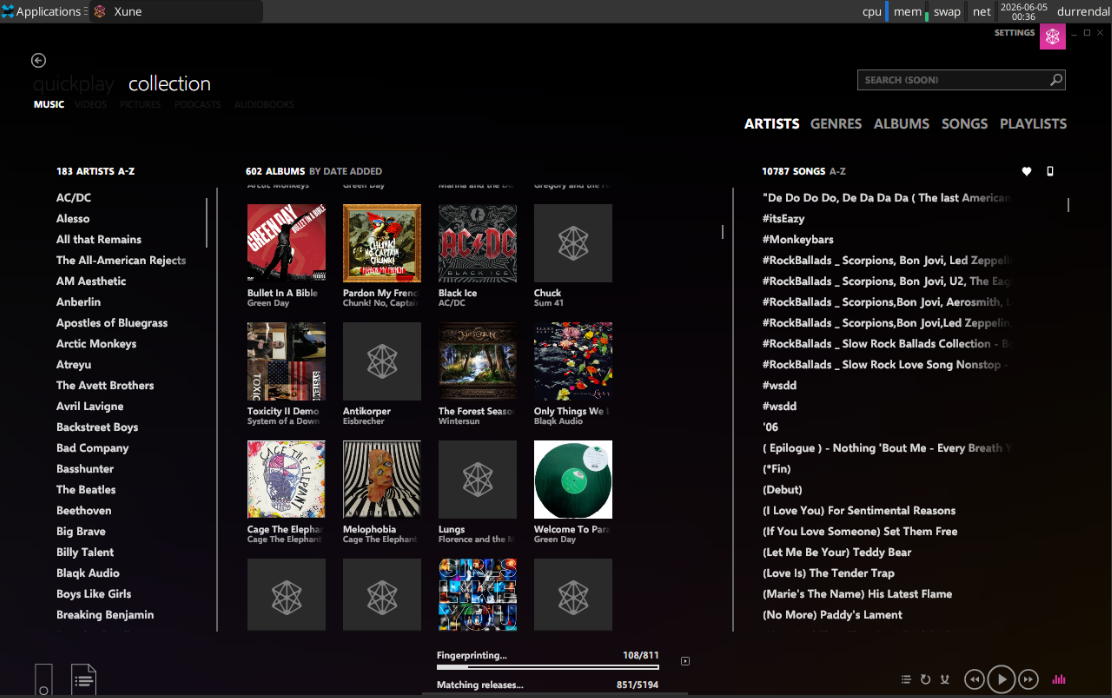
Now the software is a bit of a CPU hog, and it has OOM'd on my little 8GB RAM VM once, but despite those sharp edges it legit just works. I'm even able to to sync music from the VM onto my Zune via spice USB redirection at reasonable speeds. Never in my wildest dreams would I have imagined any of that would be possible, and from a setup/configuration perspective all I needed to do was install the flatpak:
flatpak remote-add --if-not-exists flathub https://flathub.org/repo/flathub.flatpakrepo
flatpak install flathub org.freedesktop.Platform//24.08
flatpak install Xune-0.2.1.1-Linux-x64.flatpak
And add some udev rules to my VM, because the official instructions to populate that using Xune didn't work for me.
# /etc/udev/rules.d/51-zune.rules
SUBSYSTEM=="usb", ATTR{idVendor}=="045e", ATTR{idProduct}=="063e", MODE="0666"
SUBSYSTEM=="usb", ATTR{idVendor}=="045e", ATTR{idProduct}=="0710", MODE="0666"
And because I'm lazy and really just want my Zune to always be accessible via USB spice to that VM, I added a usb device association for my Zune to my Xune VM.
incus config device add zune cindroj-zune usb vendorid=045e productid=0710
The net result of which is actual music magic, and the ability to rock out like it's 2009 again!
Which I started doing immediately despite it being quite late. There's no bad time for metal!